JamSpay is a skimmer and MST jammer. It was specifically design to jam and intercept Samsung Pay tokens. MST(Magnetic secure transmission) is the technology that Samsung devices implement to emulate a physical swiping card in the terminal.
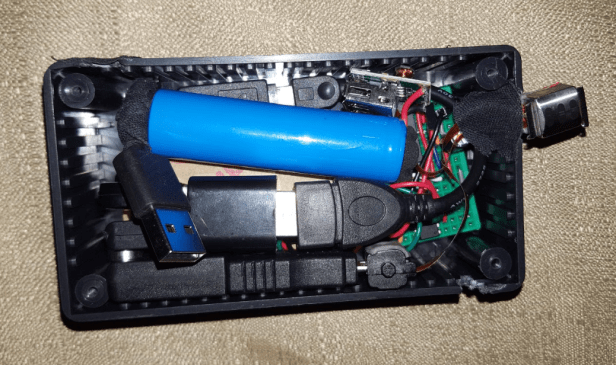
Hardware list:
– Raspberry Zero
– Lipo 5 V
– Credit Card reader one head
– MagSpoof
– USB adapters
– USB WIFI dongle
– Mini OTG USB
General Functions
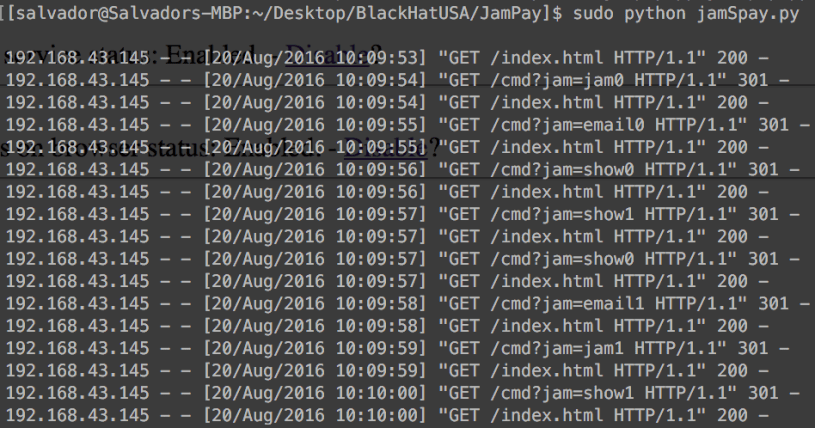
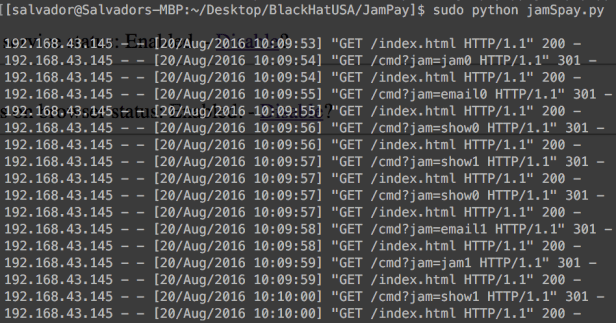
JamSpay runs a Python script when it boots up. This program executes a Python web server which is essential to control three more services: Jammer, send tokens by email and show tokens on the browser. Running a web server, the attacker is able to connect remotely to the device to enable or disable any service. The web browser page for http://spay:9999
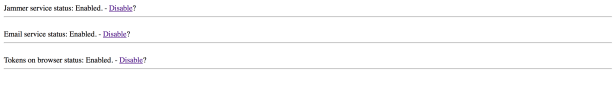
In the raspberry zero, the web server will handle all the requests and will disable or enable the services:
Ideas Behind the Hardware
To jam the MST signals, JamSpay lies in a modified MagSpoof. This MagSpoof version is directly connected on the Raspberry Zero’s GPIO to control the power flow. When the Jammer service is enabled, the Raspberry Zero releases power to the MagSpoof every three seconds. This is to keep the terminal busy as much as possible sending the same token again and again. That token is in a valid format following the ABA(American Banking Association), but it is disvalue in the monetary way. Example of this token: jamToken = ‘4097900100564980^22011011362000985128?’
The Raspberry Zero is equipped with a Magtek card reader, and it is ready to detect any token in range of 2 inches or less. If the jammer is enabled, the Raspberry Zero could detect the jammer token eventually, but the program will try to filter just the tokens that differ from the Jammer token(4097900100564980^22011011362000985128?) to have valuable Samsung Pay tokens only.
Proof of concept:
Note: I will add the code to my github during this year. Also I changed the name of my tool because I noticed that a company is implementing the same name; so to avoid confusions, I will use JamSpay.
Sal.