In this post, we will analyze the NFC protocol to find the differences between the two of the most important Android digital payment systems: Samsung Pay and Android Pay. I will not write about NFC issues or flaws. This post is about NFC communication and frameworks.
Background
Samsung Pay implements two protocols: MST and NFC. MST has some flaws and limitations. You can read my MST white paper from the Black Hat website.
In the other hand, Slawomir Jasek presented in HITB conference about the limitations of the HCE(Host Card Emulation) system that implements Android Pay to make purchases using NFC.
Idea
When you add a card to Samsung Pay or Android Pay, a framework behind scenes will enroll that card into the system. This framework could be Visa, Mastercard, Amex or other depending of the card. This process gives a tokenization process to make transactions implementing NFC.

Scenario
I will add the same Visa card in both platforms: Samsung Pay and Android Pay to see how the tokenization works. Also to demonstrate how they implement the same framework behind scenes. This could apply to other systems or platforms as well.
After I added the card in both payment methods, I will read the NFC transactions using an USB ACR122u and a modified RFIDIOt library to see the characteristics and differences.
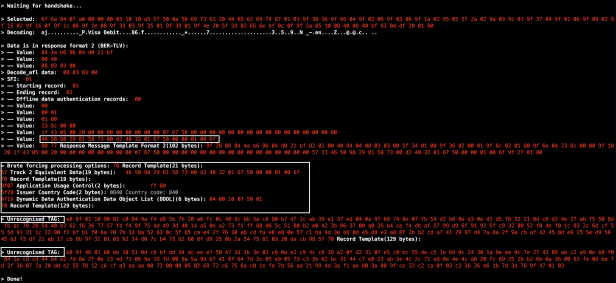
Android Pay NFC log:
If we analyze both logs, we are able to indicate that Android Pay NFC has some extra records than Samsung Pays. We could find them implementing a brute force attack against the processing options. But what exactly are these records?
The first record is an EMV Proprietary Template containing Public Key Certificate(9F46), and we can decode it:
The second record is an EMV Proprietary Template which contains Signed Dynamic Application Data(9F4B). Decoding it:
If I compare the first token from Android Pay and Samsung Pay, I can notice something interesting:
Android Pay: 46 50 98 29 81 58 73 00 d2 40 32 01 67 50 00 00 01 00 6f
Samsung Pay: 46 50 98 29 81 58 72 92 d2 40 32 01 67 50 00 00 02 37 7f
Seems that the card is a consecutive, and the difference in the last part of it is minimum. If you are asking yourself, why the Samsung Pay token starts with 02(red numbers) instead of 01 like Android Pay? It is because Samsung Pay assigned the 01 to the MST technology and for NFC 02. We can get valuable information to understand their processes.
If you want to learn more about NFC, please take a look at my post about intro to NFC.
What about Apple Pay, is it implement the same framework to add the cards?
Sal.